Don’t let Bracket’s ease of use fool you. The encryption techniques employed to secure your email data are state of the art. Bracket is built on a distributed, multi-layer AES256 encryption design with automatic key rotation. This means you never have to wonder if your data is secure.
Fully compatible with ALL email programs:
Only $8.45 per month
(Per User)
*Free Trial Available to Existing Clients Only”.
1. Multi-Layered AES256 Encryption
AES, or Advanced Encryption Standard, is a symmetric-key block cipher algorithm accepted by the U.S. and Canadian governments for securing data in transit and at rest.
Using a 256-bit block size creates a very secure key, and encryption occurs at multiple layers beginning when the message is transmitted from the sender to the encryption system, at the encryption storage point, and during transmission for a secure decryption request. Each piece of data in Bracket is encrypted multiple times in a layered approach.
To access any given piece of data (message, attachment, etc.) it is necessary to unlock several layers of encryption.


2. Individual Message Passwords
To enhance the security of individual email messages, Bracket users can add a unique password to each encrypted message either via the Bracket Console or when sending a message via their email client (i.e. Outlook 2016).
When sending an encrypted email message to a “non-private” free email address, it is strongly recommended that Financial Advisors ALWAYS use a password. This is especially true when dealing with email addresses from free email providers like gmail.com, yahoo.com, and others.)
3. Message Expiration (Auto Self-Destruct)
Because most people don’t want or need their sensitive data lingering around forever, Bracket only retains messages for a maximum of one year.
To save messages for longer, it is very simple to securely download them to your computer. On the flip side, if you would like your message to expire more quickly, you can set the message expiration for an individual message by clicking the message options icon in the top navigation when creating a new message or viewing a message you’ve already created.
Expired messages are automatically deleted from the Bracket Secure Server and are no longer accessible to you or any of the message’s recipients.
NOTE: Whenever ANY encrypted message is sent from a regular email program (Outlook, Goldmine, Kronos, Apple Mail) a copy is always stored in the SENT folder on the users PC. Copies of these outgoing messages are ALWAYS available on a Bracket users personal PC even after the copies have been deleted from the Bracket secure server.

4. Distributed Encryption Keys
Distributed encryption keys is a method by which multiple sources contribute to the creation of encryption keys.
The encryption keys used for the full encryption chain (Multi-Layered AES256 encryption) are not all stored in a single database or even physical location. They are distributed with access controls setup separately, so the access is limited to only what is necessary.
In the case of personal data keys, the registered Bracket user holds the final encryption key needed so even Bracket cannot unlock the data.


5. Two-Factor Authentication
Two Factor Authentication (TFA) is set up on the settings page in the Bracket Console. When setting up TFA, you are required to enter your mobile phone number.
Once TFA is enabled, every time you want to sign into your Bracket Console ( https://bracket.email ) to send, read or reply to secure email messages, you will sign in by requesting a sign-in link as usual, but NOW you will also be prompted to enter a randomly generated, single-use six-digit code (which is automatically delivered via SMS to your mobile device).
6. Expiring, one-time-use links
Whenever you need to log into the Bracket Console ( https://bracket.email ), you must request a one-time sign-in link, which is sent to your email address.
As an extra security measure, these one-time sign-in links expire 15 minutes after being delivered to your inbox.
In addition, each sign-in link only works once, so you never have to worry about someone rummaging through your inbox and opening old links.

7. Personal Data Key
You can tell Bracket to generate a secure personal data key from the settings page of the Bracket console ( https://bracket.email ). Your personal data key will be shown to you only during setup, at which time you will be responsible for recording your key and storing it in a safe place.
Once enabled, this unique personal data key is automatically added to the AES256 key used to encrypt every message handled by the Bracket Email Encryption system.
Your Personal Data Key will also be required every time you sign into the Bracket console to view secure messages. If you have enabled this security mechanism, it will be impossible to view your data without your personal data key.
Please note that without this key, the only way to restore your access to Bracket is to reset your account, which will permanently delete any previously existing messages.
8. Advanced Device Fingerprinting
Sign-in links will only work from the device that originally requested access. If a different device attempts to sign in, the link is invalidated and the session is blocked.
For example, when you request a sign-in link via your office PC, that device is “fingerprinted” by Bracket and this “fingerprint” is embedded inside the sign-in link that you receive in your inbox on your computer.
If you also receive a copy of the sign-in link on your mobile device and try to sign in to the Bracket console via that copy of the email, the system will block your attempt.
You will instead be given the option of requesting a one-time sign link via your mobile device.

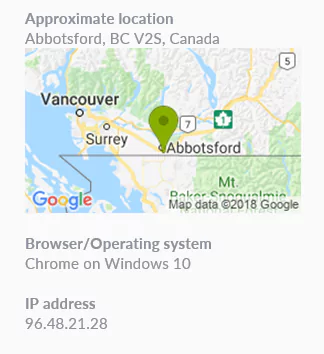
9. Geolocated Sign-In Requests
As an additional layer of security, sign-in request email notifications also include the requesting device IP and approximate location.
For example, when a Bracket user at AdvisorNet Head Office in Abbotsford, BC requests a sign-in link to their email address, the resulting notification message includes a Google map image and the IP address of the device making the request.